Archive
Articles
51 posts across 4 years
2026
10 postsOmniGen2: Unauthenticated RCE via Pickle Deserialization in BAAI's Reward Server
A critical unauthenticated RCE vulnerability in OmniGen2's reward server infrastructure. The Flask-based servers deserialize raw HTTP POST bodies with pickle.loads() without any authentication, giving instant code execution to anyone with network access.
sglang: Unauthenticated RCE via Pickle Deserialization in ZMQ Transport (Disaggregated Serving)
A critical unauthenticated RCE vulnerability in sglang's ZMQ transport layer for disaggregated serving. ZMQ PULL sockets bind to all interfaces and deserialize messages with pickle.loads() - no auth, no validation. Distinct from CVE-2025-10164 which only covers the HTTP API.
openDCIM: From SQL Injection to RCE via Config Poisoning
Three chained vulnerabilities in openDCIM turn a missing authorization check into unauthenticated remote code execution on Docker deployments.
CVE-2026-27743 through CVE-2026-27747: Five Vulnerabilities in SPIP Plugins
Five vulnerabilities across SPIP plugins: two SQL injections, two RCE (one unauth, one auth), and reflected XSS. Same template engine, same mistakes, different entry points.
CVE-2025-71243: AI-Assisted Reversal of SPIP Saisies RCE in 30 Minutes
From VulnCheck advisory to working PoC in 30 minutes. Full AI-assisted reversal of CVE-2025-71243, an unauthenticated PHP code injection in SPIP's Saisies plugin affecting versions 5.4.0 through 5.11.0.
MajorDoMo Revisited: What I Missed in 2023
In 2023 I found CVE-2023-50917 in MajorDoMo. In 2026, AI agents found 8 more bugs I completely missed.
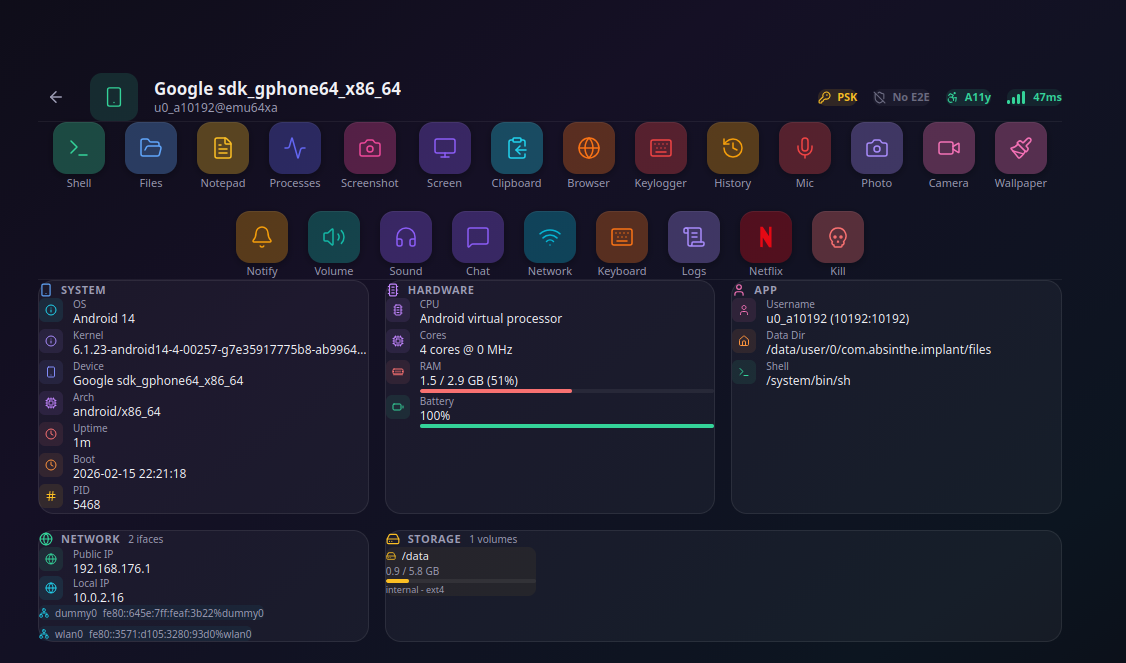
Android's AccessibilityService: A Single Toggle to Total Device Control
How one API designed for disability access became the foundation of a $145M surveillance industry. A proof-of-concept implant demonstrates the full attack chain: silent permission escalation in 2.4 seconds, contextual keylogging, see-through overlays, network toggle, self-hiding persistence, and an embedded Linux terminal with apt - all from a single accessibility toggle, no root required.
LightLLM: Unauthenticated RCE via Pickle Deserialization in WebSocket Endpoints
CVE-2026-26220: A critical unauthenticated RCE vulnerability in LightLLM's PD disaggregation system. Two WebSocket endpoints deserialize binary frames with pickle.loads() without authentication, and the server explicitly refuses to bind to localhost - it's always network-exposed.
manga-image-translator: Unauthenticated RCE via Pickle Deserialization with Nonce Bypass
A critical unauthenticated RCE vulnerability in manga-image-translator. Two FastAPI endpoints deserialize raw HTTP POST bodies with pickle.loads(), and the nonce-based authentication is bypassed because the default value is an empty string - which is falsy in Python.
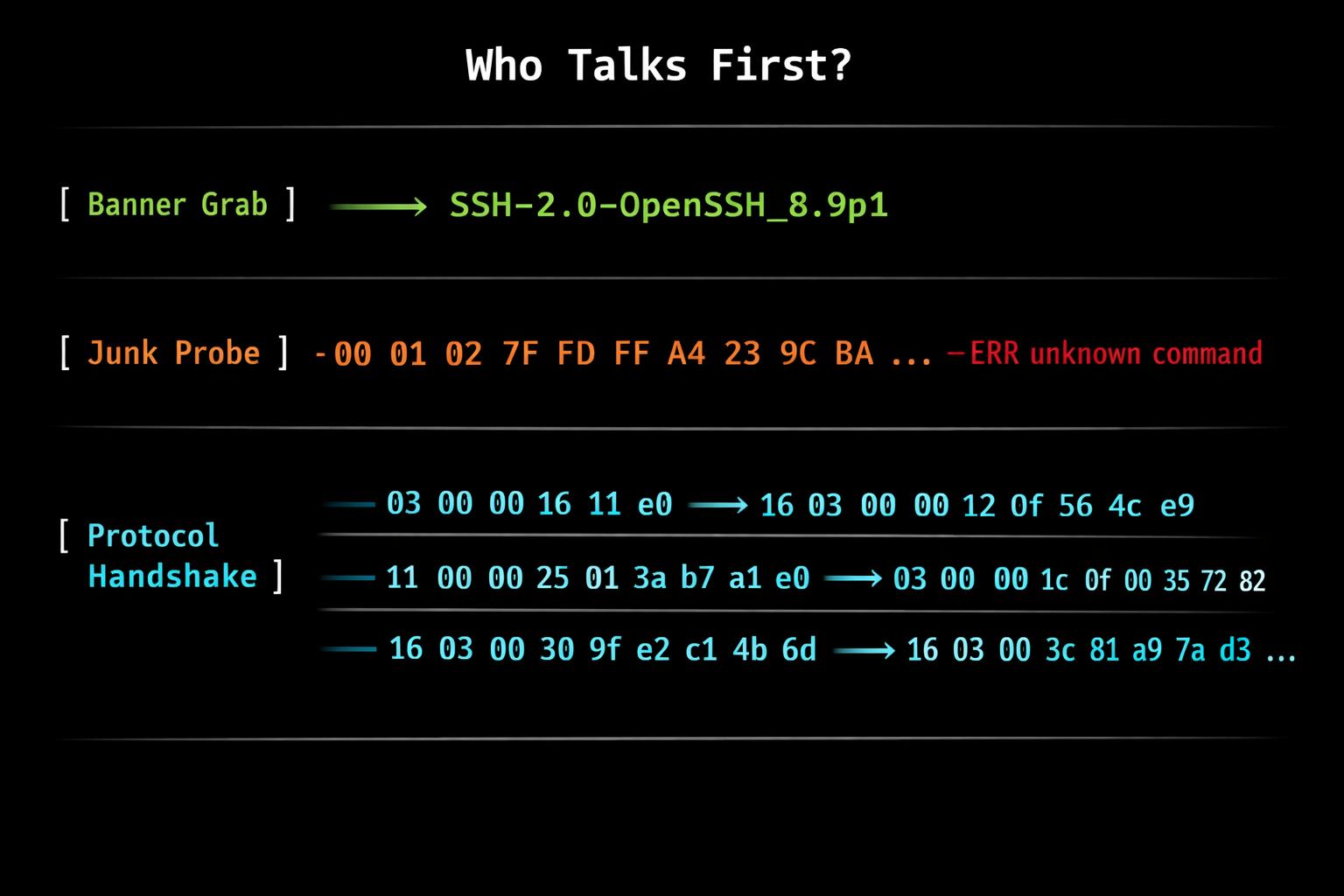
How Internet Scanners Actually Work: The 'Passive' Scanning Myth
A deep dive into how internet-wide scanners like Shodan, Censys, and nmap actually identify services. Spoiler: there's nothing passive about it.
2025
12 posts
From Zero to Shell: Hunting Critical Vulnerabilities in AVideo
A comprehensive security audit of AVideo revealing 10 vulnerabilities including a critical unauthenticated RCE that chains cryptographic weaknesses, predictable salt bruteforce, and an eval() vulnerability to achieve complete server compromise in under 10 seconds.
Streama Path Traversal + SSRF: Chaining Vulnerabilities for Arbitrary File Write
A critical vulnerability in Streama allows authenticated users to write arbitrary files through a combination of Server-Side Request Forgery (SSRF) and Path Traversal. This write-up covers the root cause analysis, exploitation flow, and the vendor's comprehensive fix.
Setting Up Giscus: An Ad-Free Alternative to Disqus for Blog Comments
How I set up Giscus for ad-free blog comments using GitHub Discussions, avoiding Disqus due to ads and other concerns.

When a Wi-Fi SSID Gives You Root on an MT02 Repeater – Part 2
Deep dive into bind‐shell deployment, payload experiments, and a new ‘time_conf’ primitive for stealthy, persistent root access without reboot or UI lockup.

When a Wi-Fi SSID Gives You Root on an MT02 Repeater
How a €5 MT02 Wi-Fi repeater let me pop a root shell with nothing more than a cheeky SSID.

Multiple Vulnerabilities in Xorcom CompletePBX 5.2.35: RCE, File Disclosure and XSS
Several critical vulnerabilities discovered in Xorcom CompletePBX 5.2.35, including authenticated file disclosure, remote command execution as root, file deletion, and reflected XSS. This write-up details the black-box methodology, PoCs, and patch timeline.
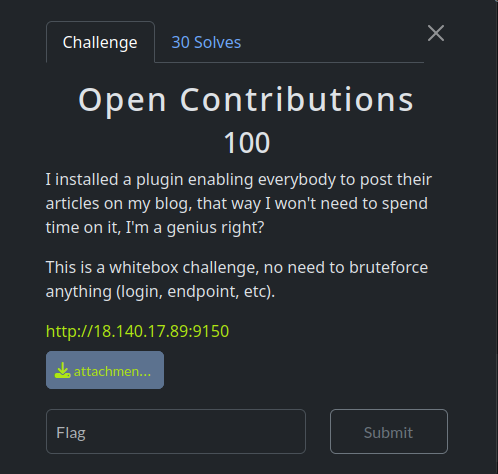
Patchstack WCEU CTF – Open Contributions
Two missing checks inside the Open Contributions plugin let any fresh WordPress subscriber escalate to contributor and read arbitrary files — including the CTF flag — without brute-forcing a thing.
Helping Friends Learn Cybersecurity: Lessons from Teaching Beginners

Vembu BDRSuite: Unauth XSS, Weird Endpoints and Silent Patches (≤ 7.5.0.1)
Analysis of two unauthenticated XSS vulnerabilities and silently patched issues in Vembu BDRSuite up to version 7.6.0. Includes PoCs, API traces, patch timeline and commentary.

WPProbe: A Pragmatic Approach to Detecting WordPress Plugins
WPProbe is a lightweight tool that leverages the WordPress REST API to detect installed plugins passively. This post covers its design, use cases, technical constraints, and how it helps avoid noisy scans.
Two Stored XSS in MagnusBilling: From CTF Curiosity to CVEs
Two Stored XSS vulnerabilities discovered in MagnusBilling 7.x, including one unauthenticated, initially spotted during a CTF. This write-up covers the discovery process, PoCs, impact, patch timeline, and thoughts on the overall codebase.
How I Got Hacked: A Warning about Malicious PoCs
An in-depth forensic analysis of how a seemingly legitimate Proof-of-Concept (PoC) for CVE-2020-35489 turned out to be a cleverly disguised malware. This blog post details the attack vector, payload deobfuscation, Indicators of Compromise (IoCs), and the steps taken to analyze and neutralize the threat.
2024
4 posts
Wikimedia/svgtranslate 2.0.1 Remote Code Execution
Analysis of Unauthenticated Remote Command Execution Vulnerability in Wikimedia/svgtranslate

Exploring Mocodo Vulnerabilities: A Compilation of CVEs from 2024
A Detailed Analysis of Two Critical Remote Command Execution Vulnerabilities in Mocodo: Implications and Fixes

Exploring AVideo Vulnerabilities: A Deep Dive into CVE-2024-31819
A technical analysis of CVE-2024-31819, uncovering a critical Remote Code Execution vulnerability in the AVideo platform's WWBNIndex plugin.

Exploring DerbyNet Vulnerabilities: A Compilation of CVEs from 2024
A Comprehensive Analysis of Ten Critical Vulnerabilities in DerbyNet v9.0: From Cross-Site Scripting to SQL Injection
2023
25 posts
CVE-2023-50917
Deep Dive: CVE-2023-50917 - Unmasking an Unauthenticated Remote Code Execution Flaw in MajorDoMo's Thumb Module
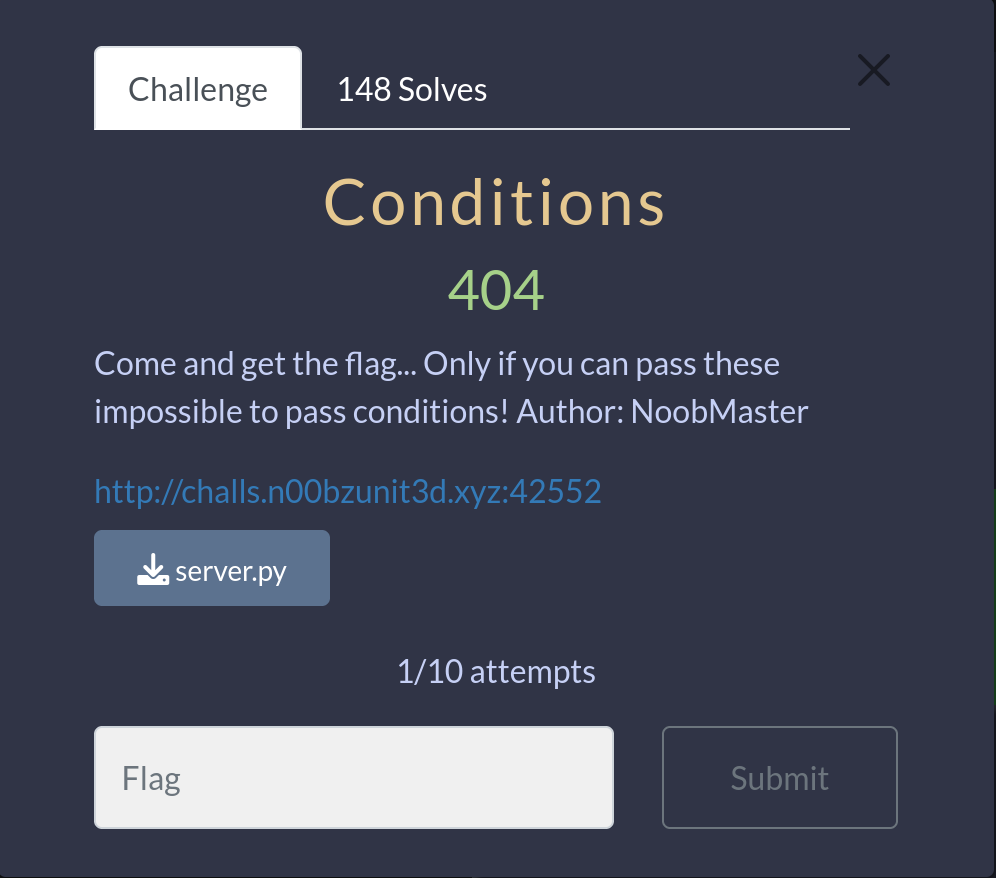
n00bzCTF 2023 - Conditions
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Conditions' presented at n00bzCTF 2023.
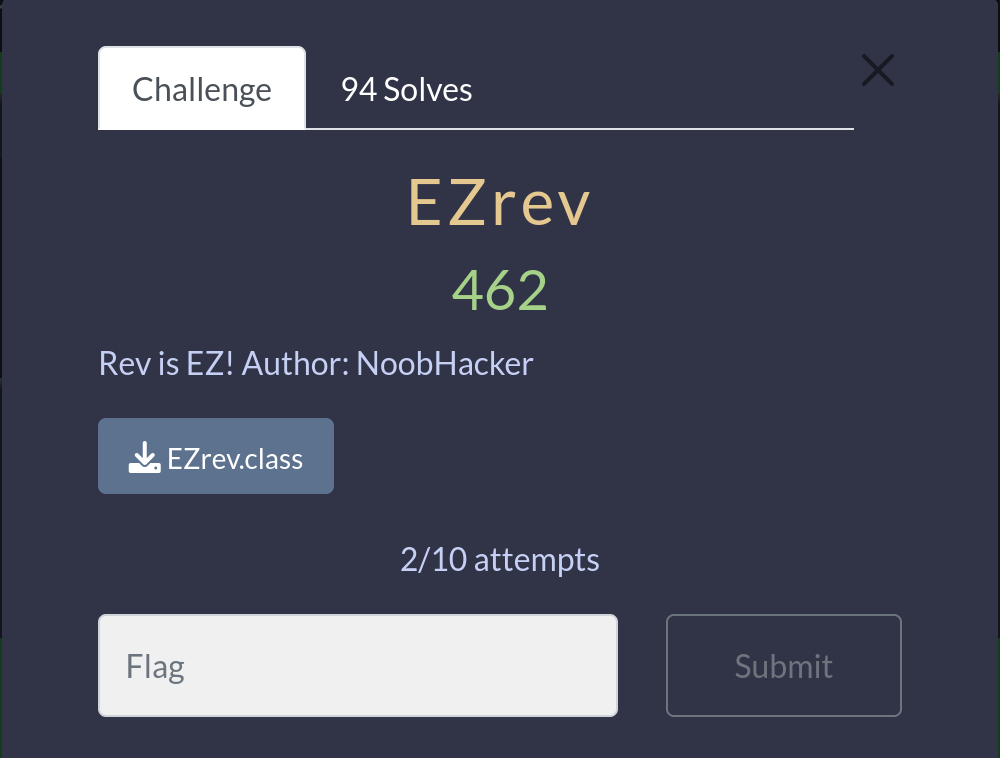
n00bzCTF 2023 - EZrev
In this article, we will explore the step-by-step walkthrough of the Reverse challenge 'EZrev' presented at n00bzCTF 2023.

n00bzCTF 2023 - MyPin
In this article, we will explore the step-by-step walkthrough of the Reverse challenge 'MyPin' presented at n00bzCTF 2023.
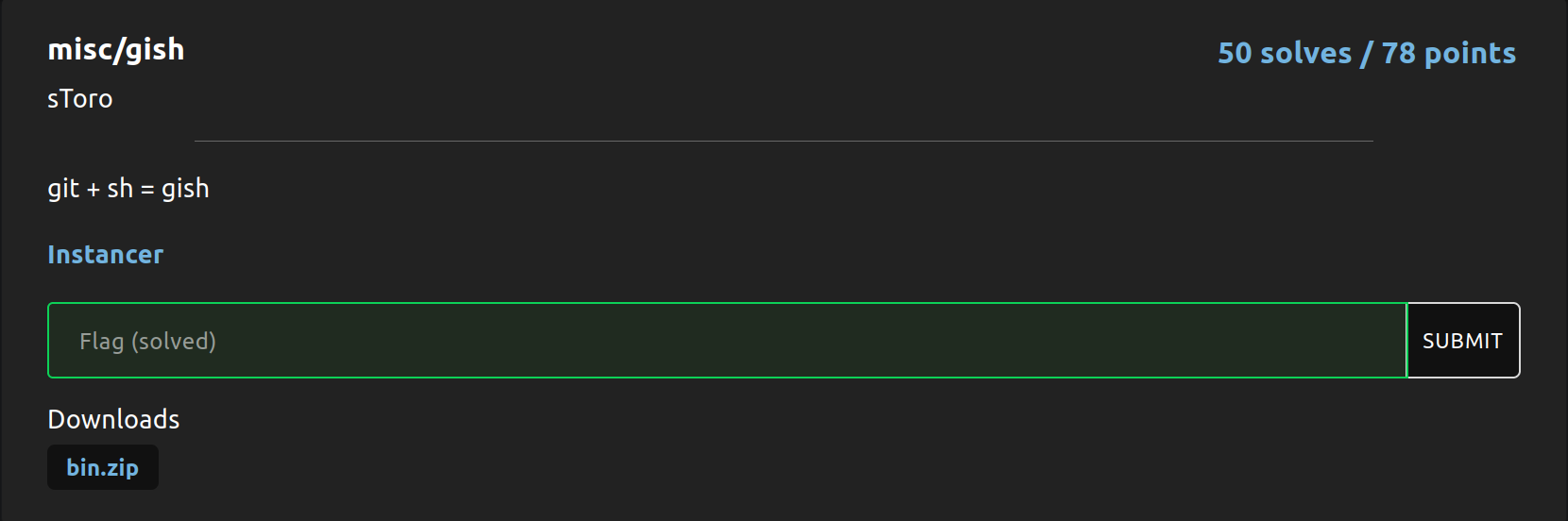
tjCTF 2023 - Gish
In this article, we will explore the step-by-step walkthrough of the MISC challenge 'Gish' presented at tjCTF 2023.
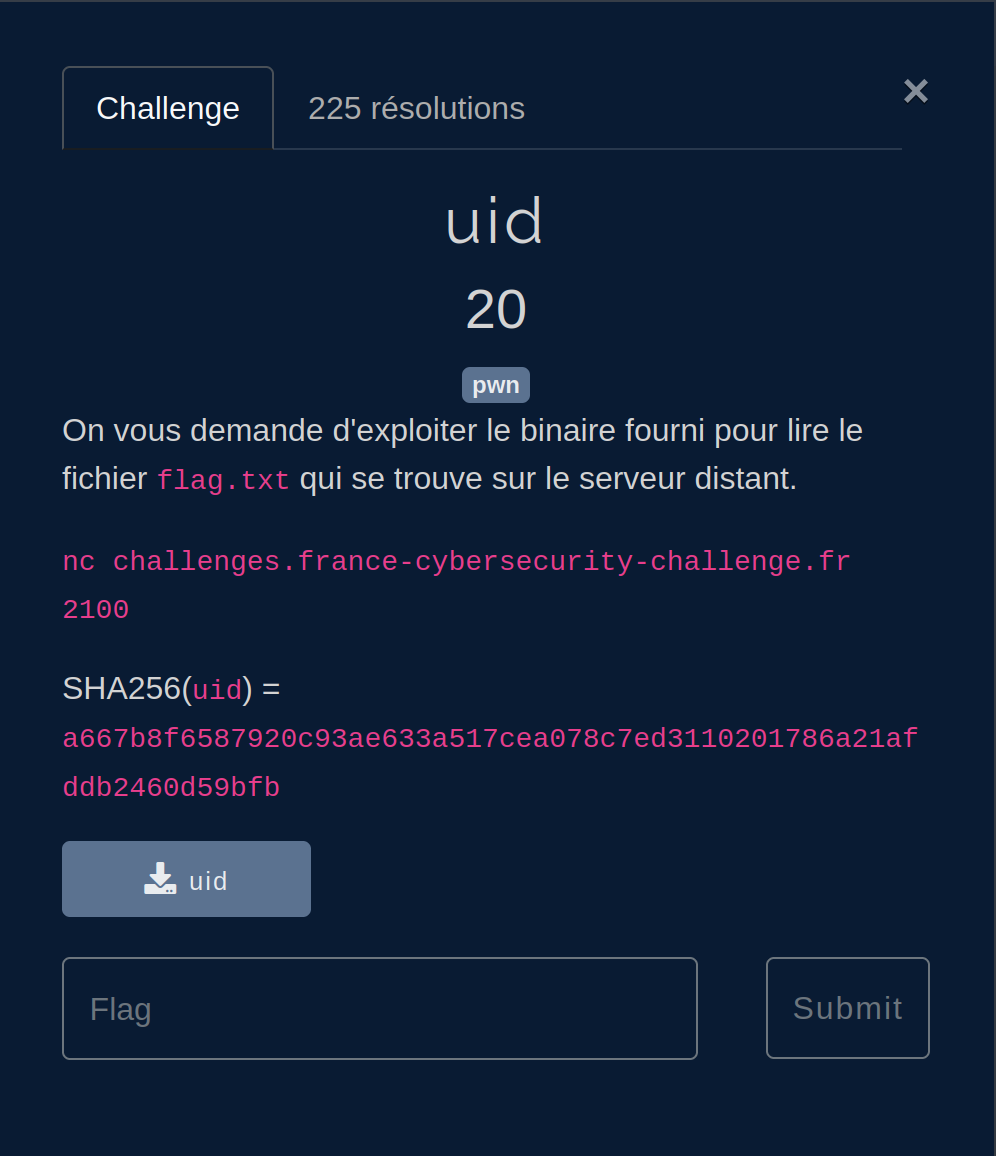
FCSC 2023 - UID
In this article, we will explore the step-by-step walkthrough of the 'uid' challenge presented at FCSC 2023.
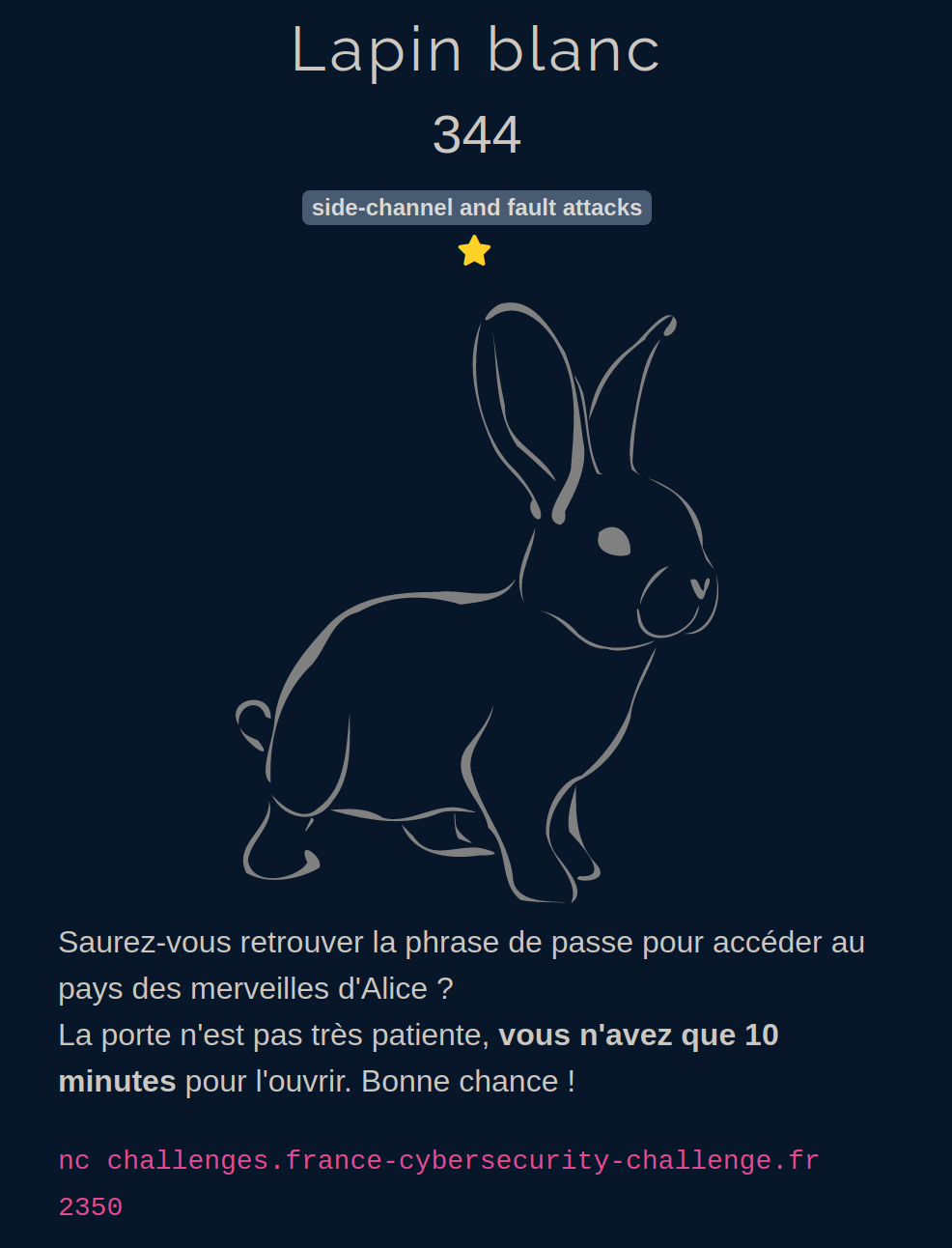
FCSC 2023 - Lapin Blanc
In this article, we will explore the step-by-step walkthrough of the 'Lapin Blanc' challenge presented at FCSC 2023.

FCSC 2023 - Zéro Pointé
In this article, we will explore the step-by-step walkthrough of the 'Zéro Pointé' challenge presented at FCSC 2023.
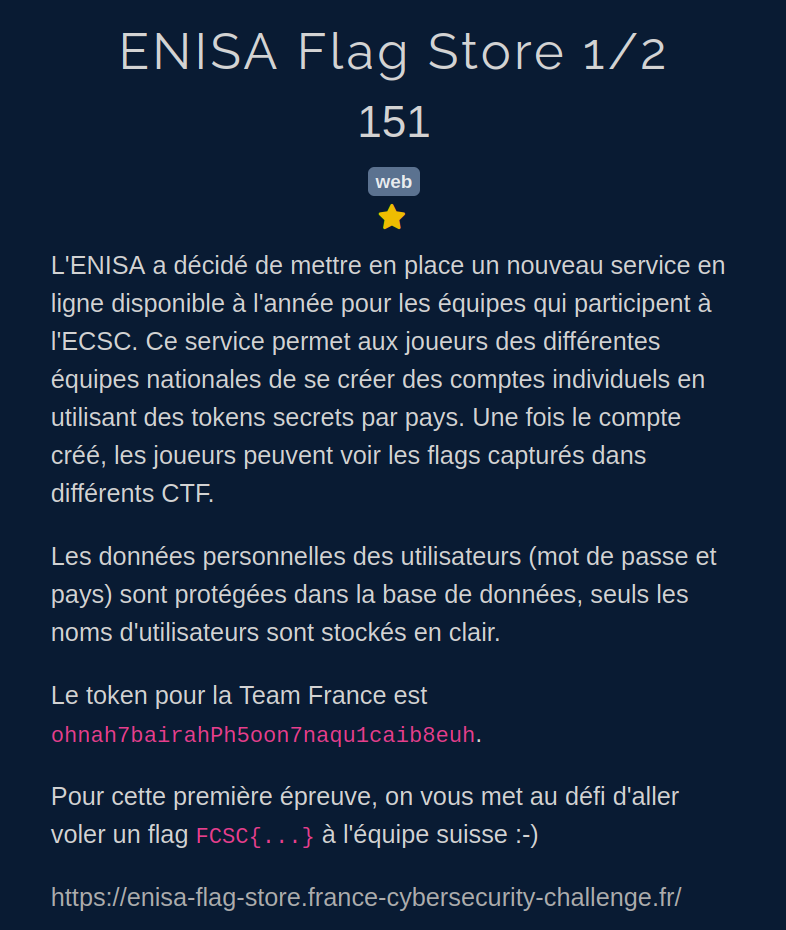
FCSC 2023 - ENISA Flag Store 1/2
In this article, we will explore the step-by-step walkthrough of the 'ENISA Flag Store 1/2' challenge presented at FCSC 2023.
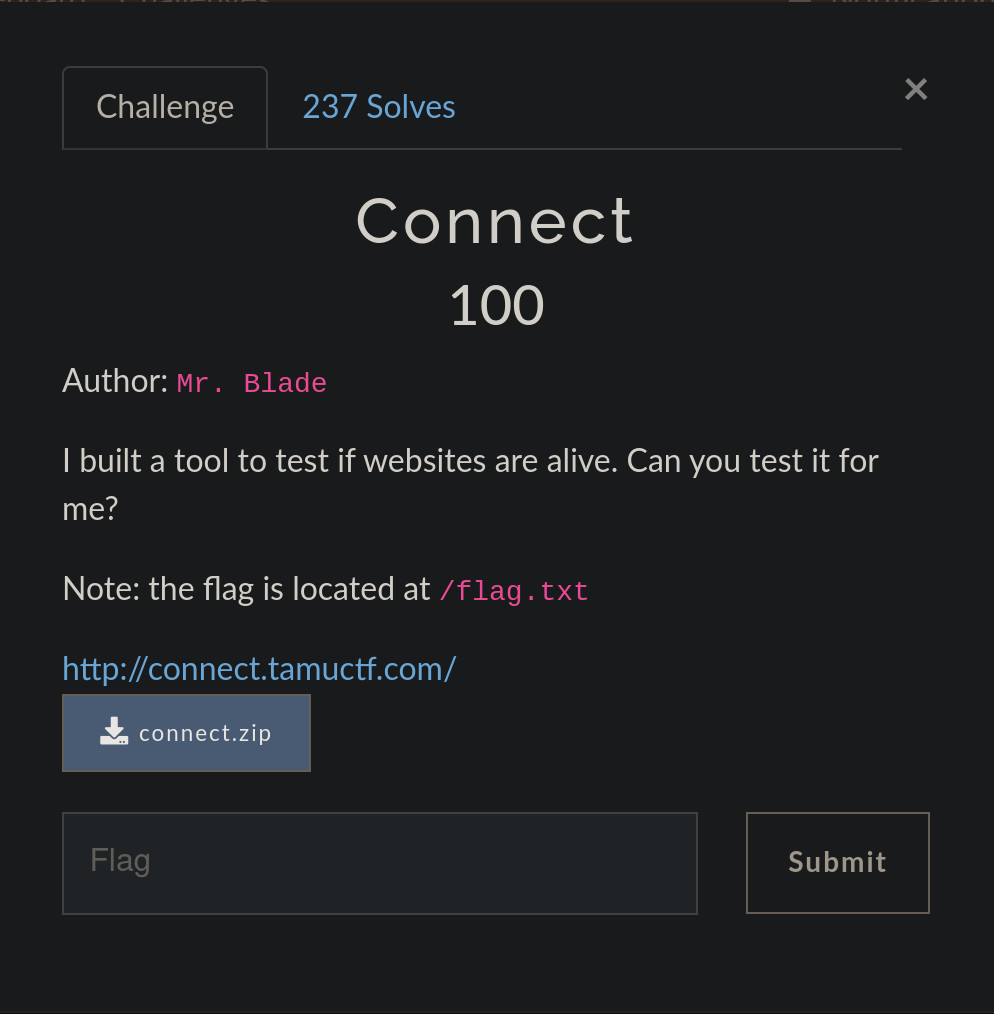
TamuCTF 2023 - Connect
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Connect' presented at TamuCTF 2023.
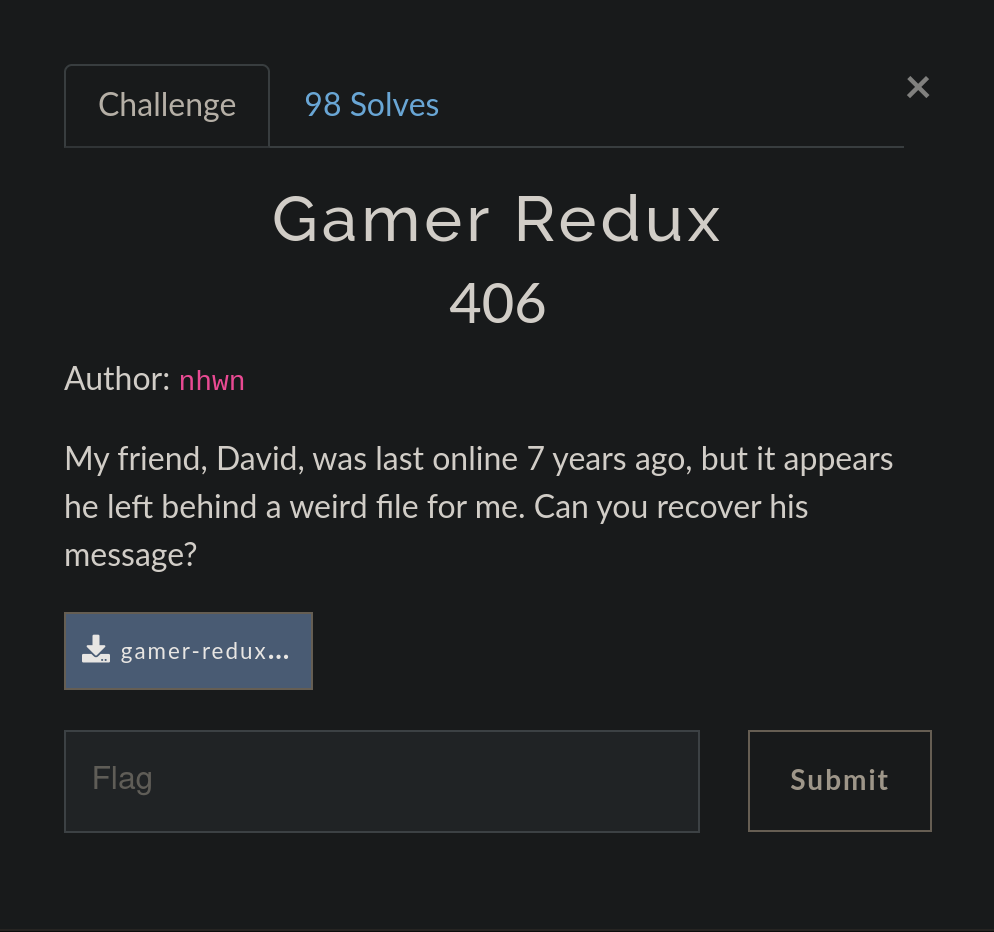
TamuCTF 2023 - Gamer Redux
In this article, we will explore the step-by-step walkthrough of the MISC challenge 'Gamer Redux' presented at TamuCTF 2023.
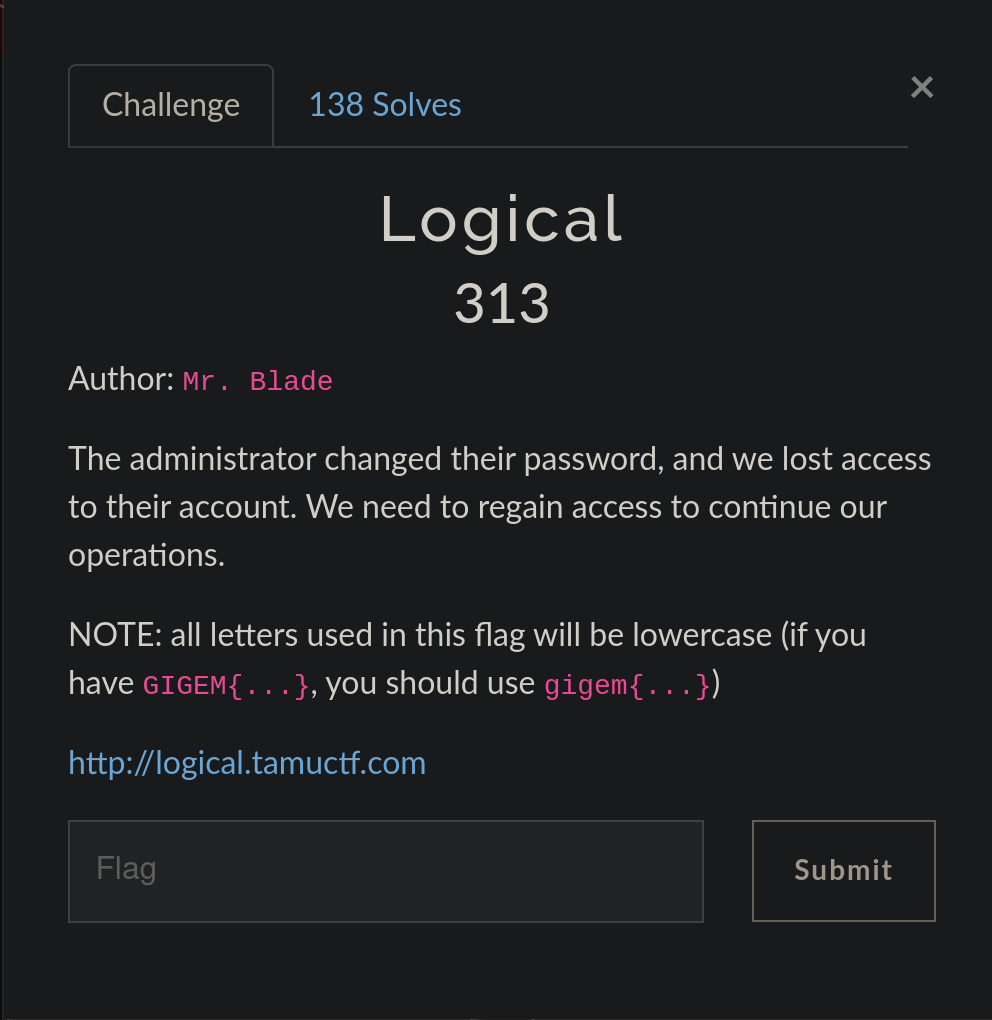
TamuCTF 2023 - Logical
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Logical' presented at TamuCTF 2023.
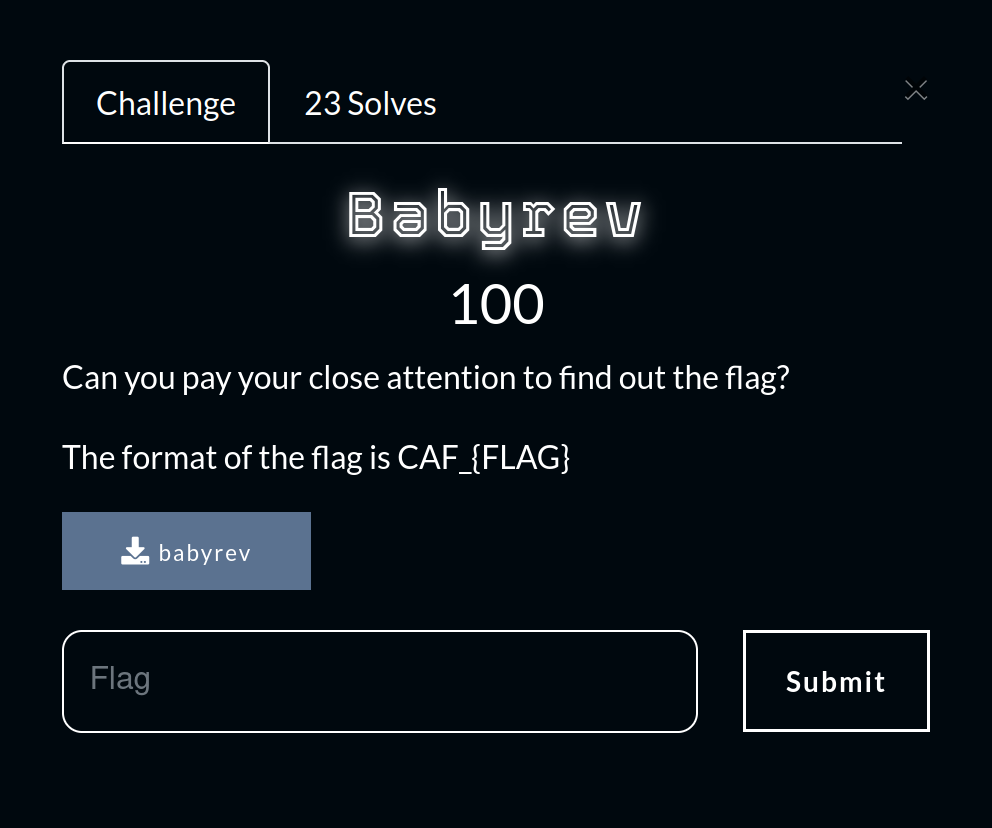
CAF 2023 - Babyrev
In this article, we will explore the step-by-step walkthrough of the Reverse challenge 'BabyRev' presented at the CTF Cyber Africa Forum 2023.

CAF 2023 - Tower of Encryption
In this article, we will explore the walkthrough of the Cryptography challenge 'Tower of Encryption' presented at the CTF Cyber Africa Forum 2023.
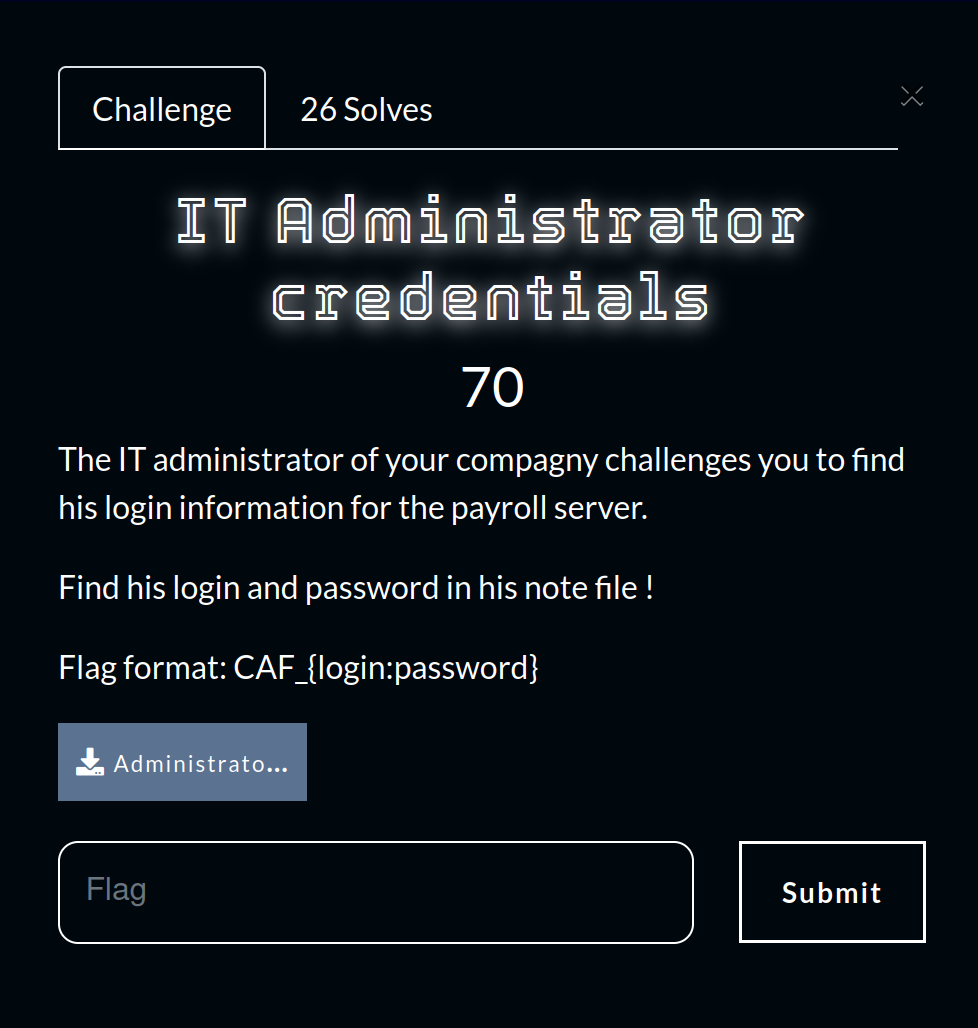
CAF 2023 - IT Administrator Credentials
In this article, we will explore the walkthrough of the Steganography challenge 'IT Administrator Credentials' presented at the CTF Cyber Africa Forum 2023.
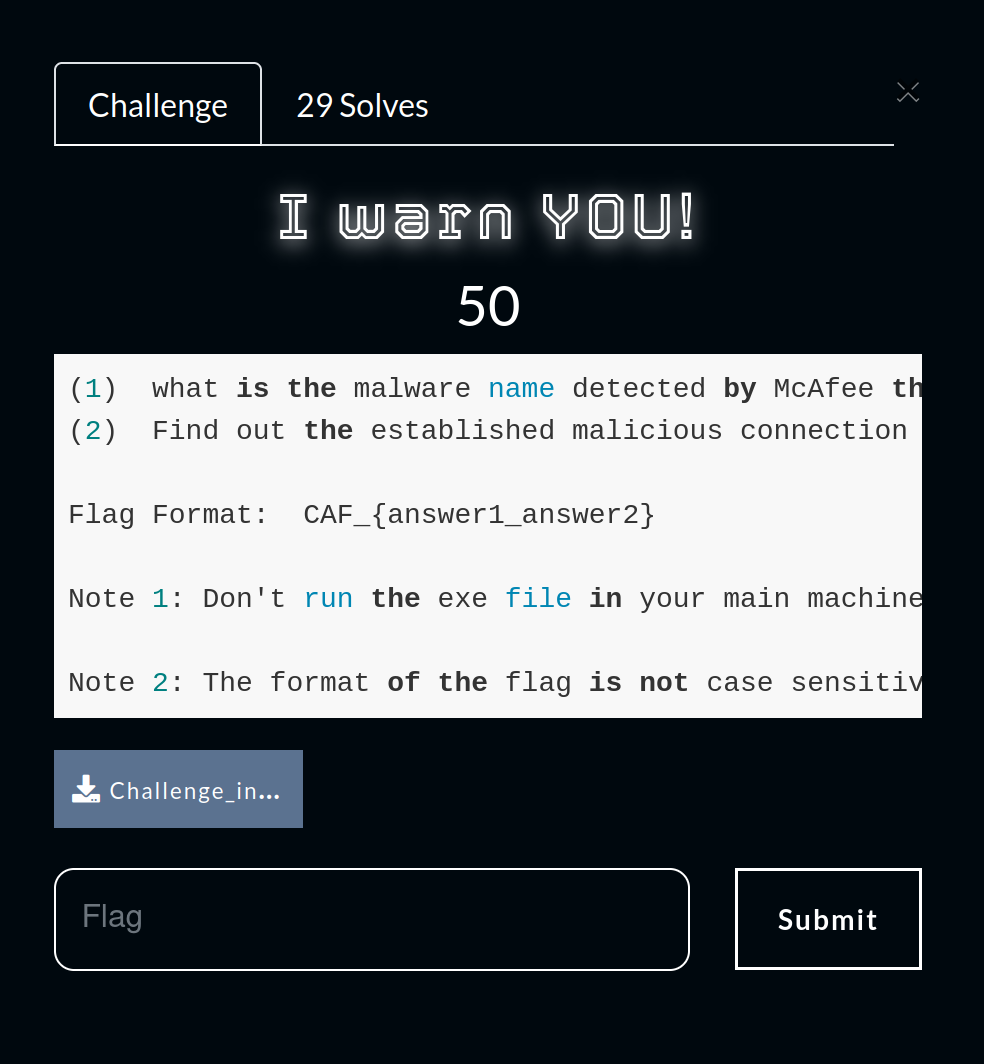
CAF 2023 - I Warn You
In this article, we will explore the step-by-step walkthrough of the Digital Forensic challenge 'I Warn You!' presented at the CTF Cyber Africa Forum 2023.
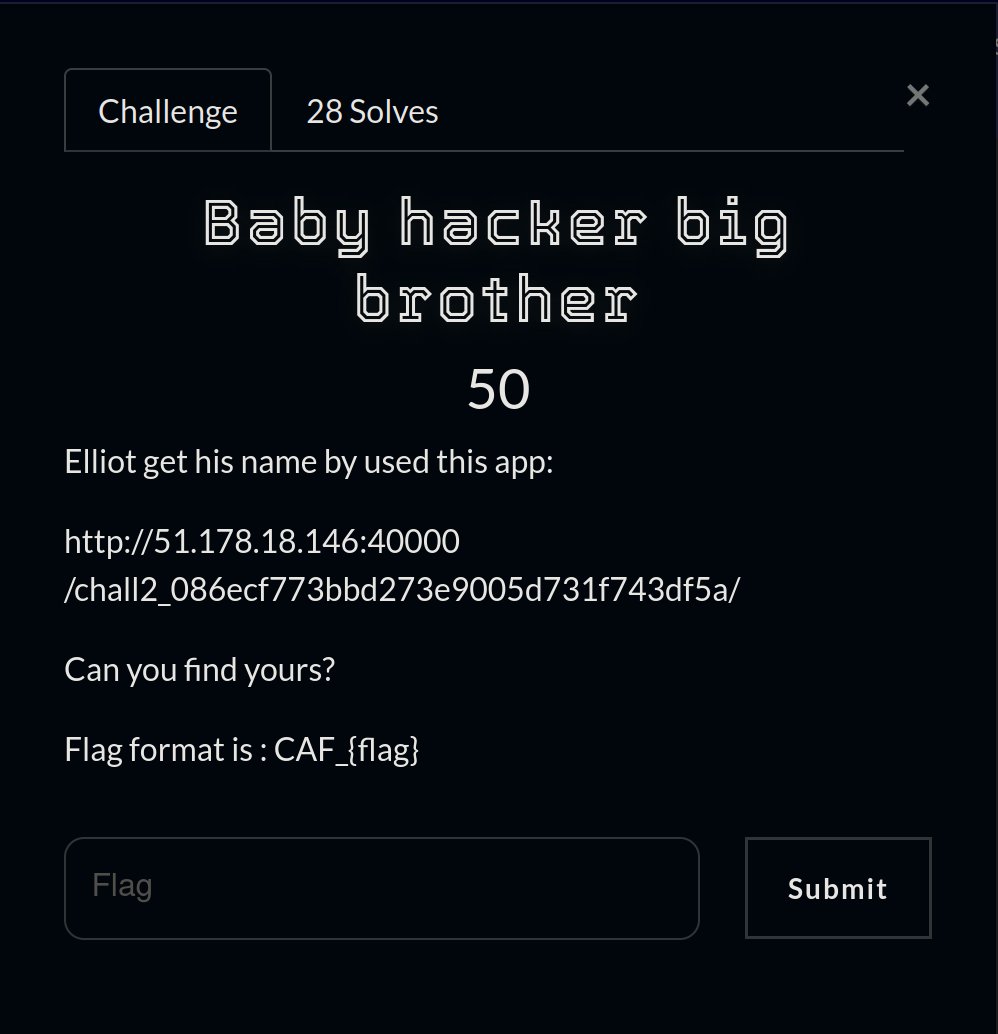
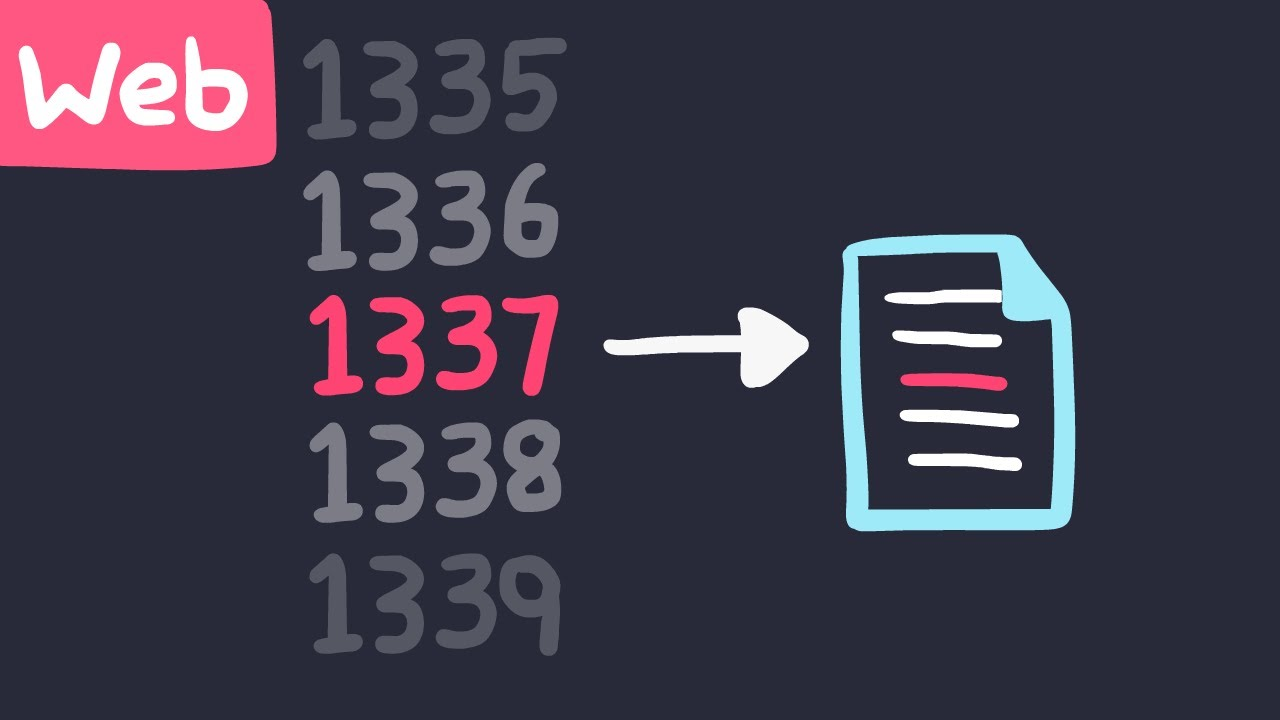
CAF 2023 - Baby Hacker Big Brother
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Baby Hacker Big Brother' presented at the CTF Cyber Africa Forum 2023.
IDOR Vulnerability: Explanation, Exploitation, and Prevention
In this article, we will explore the Insecure Direct Object Reference (IDOR) vulnerability, a common security vulnerability in web applications that can have significant impacts on data confidentiality, integrity, and availability.
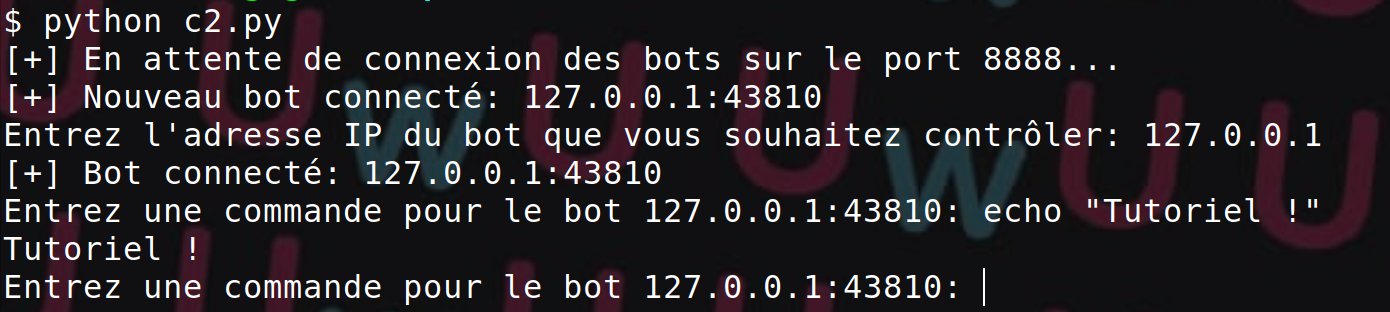
Using Python Sockets for Offensive Security
In this article, we will explore how to use Python sockets in the context of offensive security
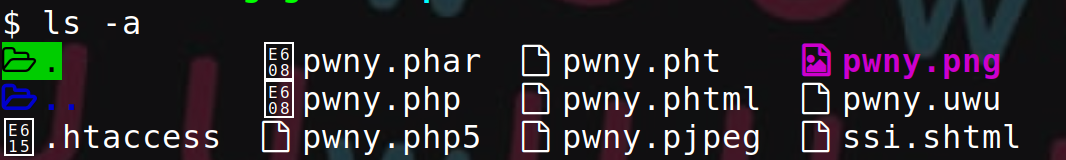
Upload Vulnerabilities: Understanding, Exploiting, and Fixing
This article presents the various variants of the 'upload vulnerability' and how to protect against them.
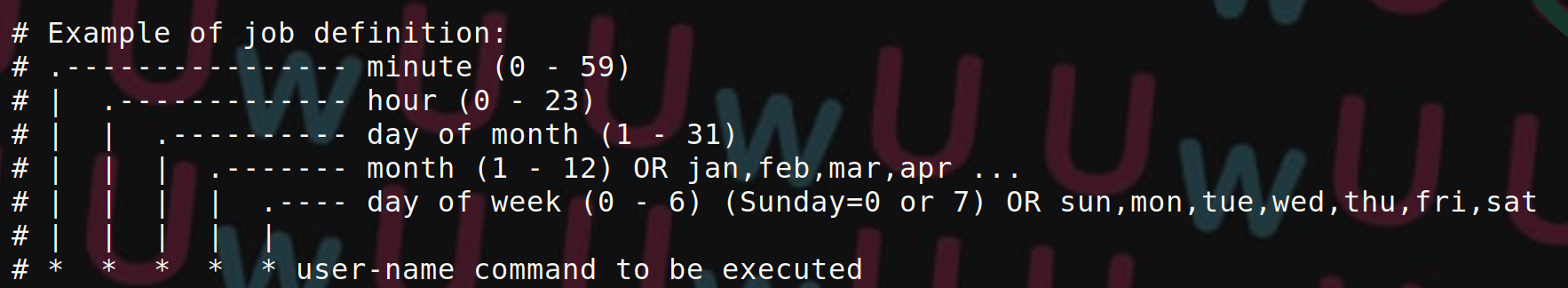
Privilege Escalation on Unix Systems via Crontab
This article demonstrates how to exploit privilege escalation from insecure scheduled tasks.

What is a Command Injection?
This article explains what command injection is, how to exploit it, and how to reduce the risks of this attack.

Configuring an Apache Server with SSL/TLS Hardening
This post explains how to secure an Apache server with SSL/TLS hardening and best practices.

Creating a Shodan Dork Using MMH3 Hash
This article explains how to create a Shodan dork based on the `favicon.ico` file using MMH3 hash

Oteria Cyber Cup 2022
In this post, I will write 2 writeups from the 'Applicatif' category, 1 and 2, both being Easy level Buffer Overflow challenges.