MajorDoMo Revisited: What I Missed in 2023
In 2023 I found CVE-2023-50917 in MajorDoMo. In 2026, AI agents found 8 more bugs I completely missed.

Wikimedia/svgtranslate 2.0.1 Remote Code Execution
Analysis of Unauthenticated Remote Command Execution Vulnerability in Wikimedia/svgtranslate

Exploring Mocodo Vulnerabilities: A Compilation of CVEs from 2024
A Detailed Analysis of Two Critical Remote Command Execution Vulnerabilities in Mocodo: Implications and Fixes

Exploring DerbyNet Vulnerabilities: A Compilation of CVEs from 2024
A Comprehensive Analysis of Ten Critical Vulnerabilities in DerbyNet v9.0: From Cross-Site Scripting to SQL Injection

CVE-2023-50917
Deep Dive: CVE-2023-50917 - Unmasking an Unauthenticated Remote Code Execution Flaw in MajorDoMo's Thumb Module
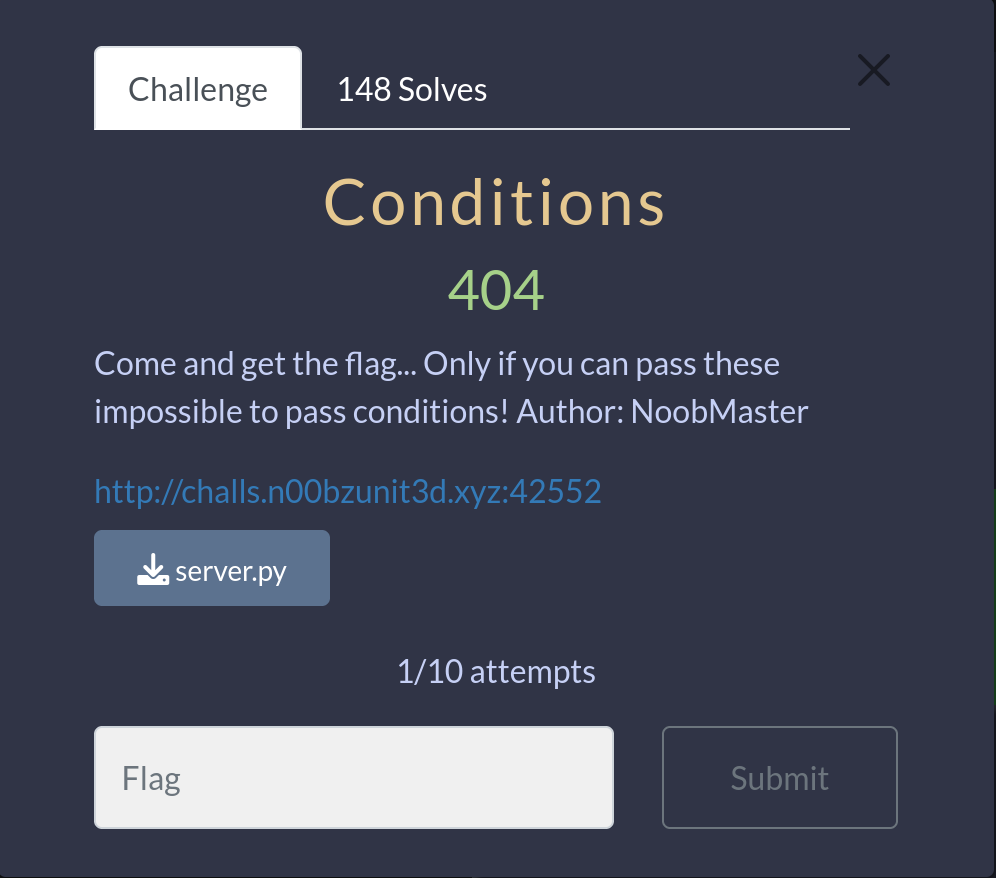
n00bzCTF 2023 - Conditions
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Conditions' presented at n00bzCTF 2023.
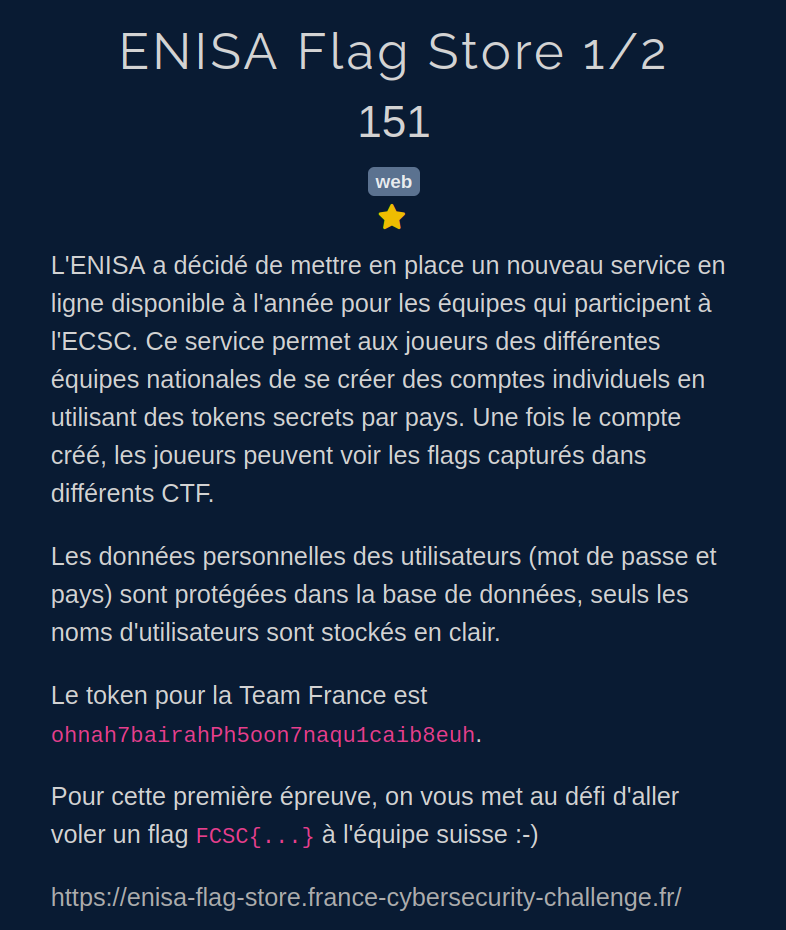
FCSC 2023 - ENISA Flag Store 1/2
In this article, we will explore the step-by-step walkthrough of the 'ENISA Flag Store 1/2' challenge presented at FCSC 2023.
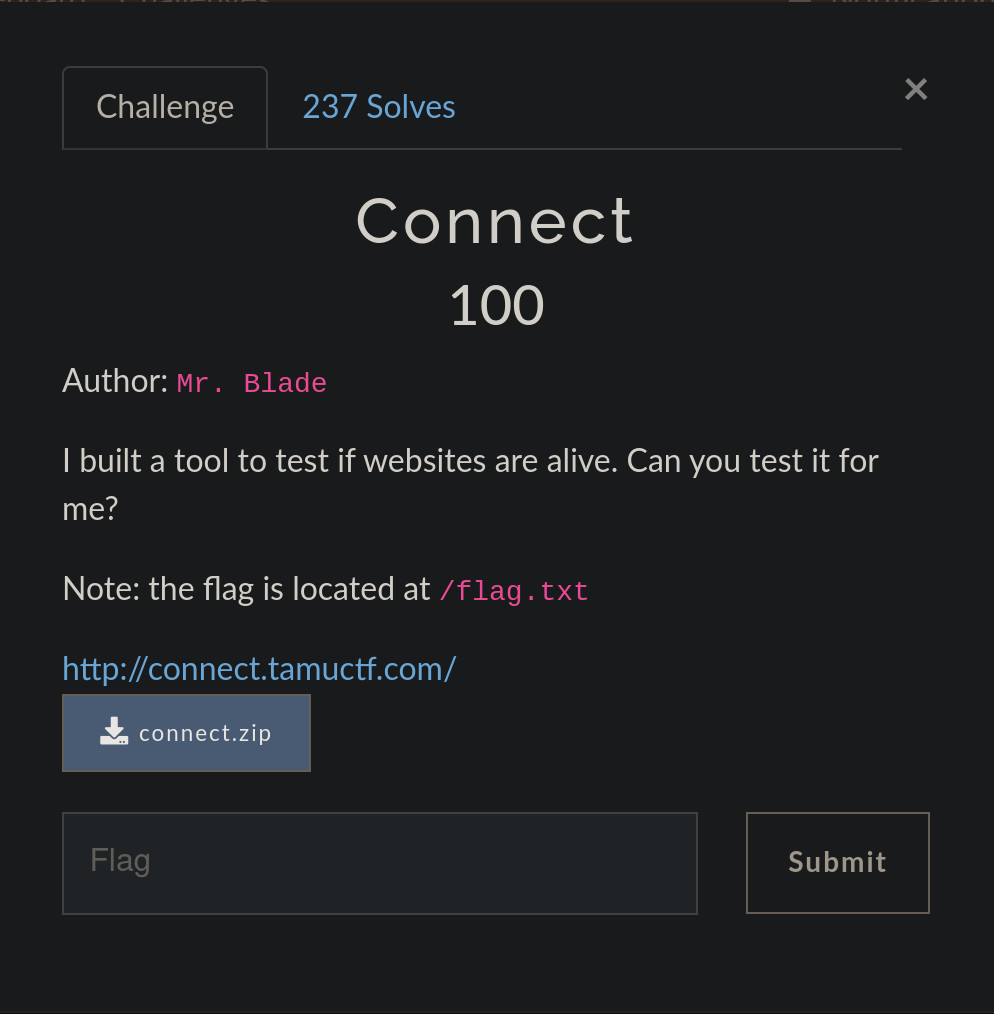
TamuCTF 2023 - Connect
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Connect' presented at TamuCTF 2023.
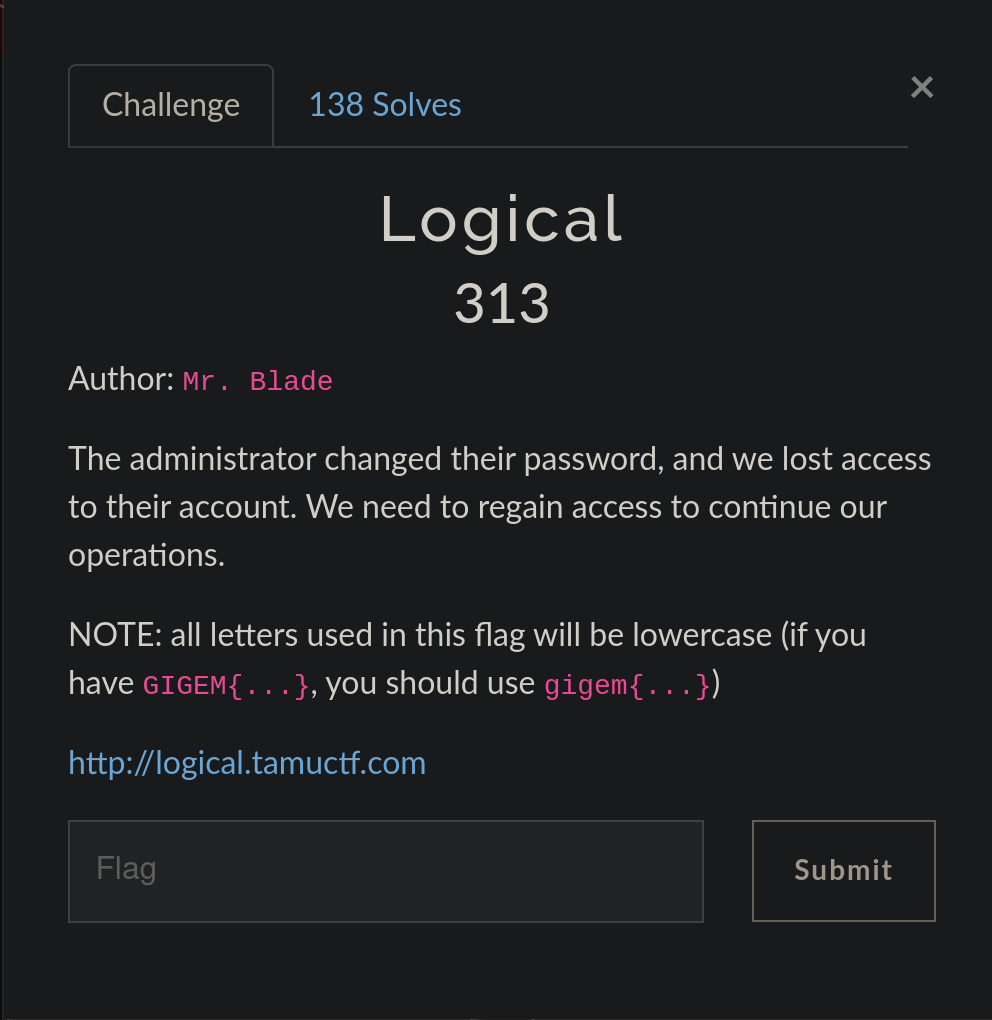
TamuCTF 2023 - Logical
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Logical' presented at TamuCTF 2023.
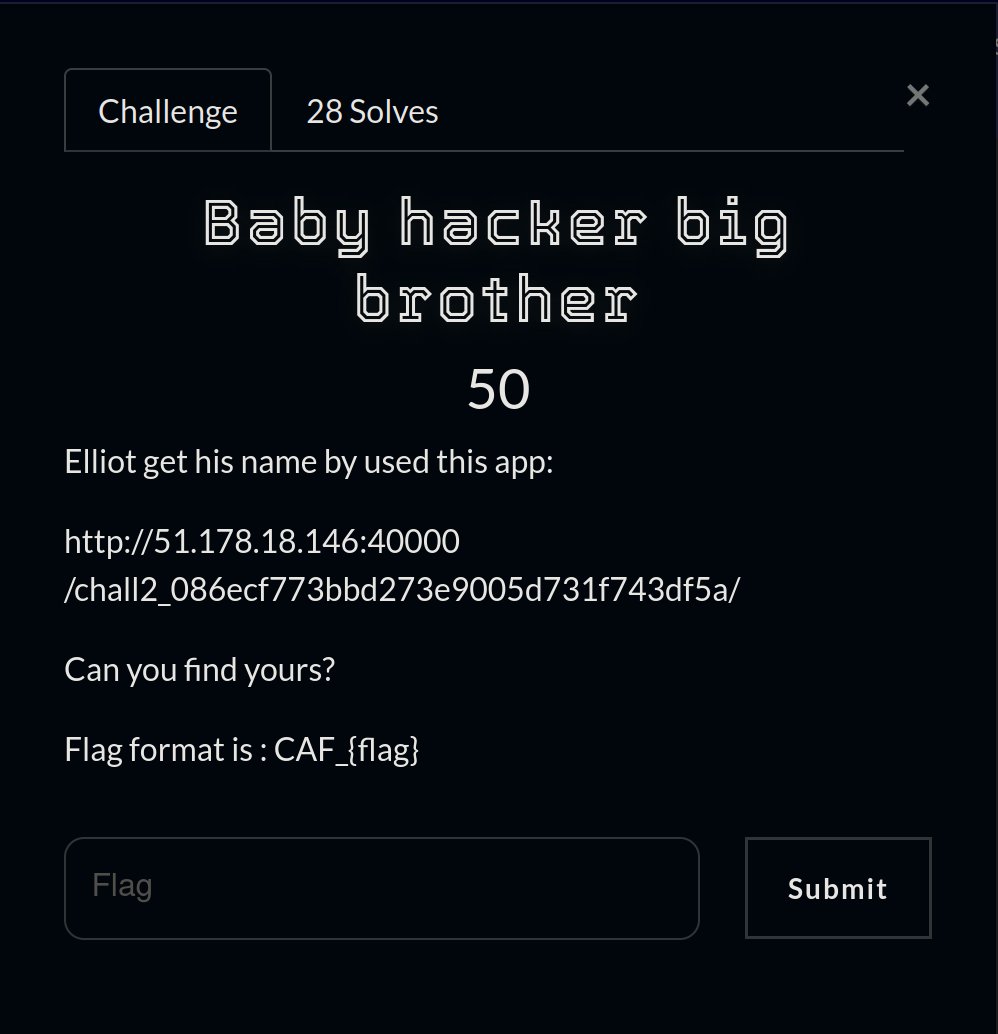
CAF 2023 - Baby Hacker Big Brother
In this article, we will explore the step-by-step walkthrough of the Web challenge 'Baby Hacker Big Brother' presented at the CTF Cyber Africa Forum 2023.
IDOR Vulnerability: Explanation, Exploitation, and Prevention
In this article, we will explore the Insecure Direct Object Reference (IDOR) vulnerability, a common security vulnerability in web applications that can have significant impacts on data confidentiality, integrity, and availability.
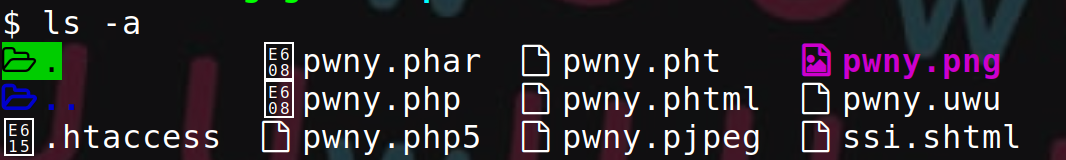
Upload Vulnerabilities: Understanding, Exploiting, and Fixing
This article presents the various variants of the 'upload vulnerability' and how to protect against them.

What is a Command Injection?
This article explains what command injection is, how to exploit it, and how to reduce the risks of this attack.

Configuring an Apache Server with SSL/TLS Hardening
This post explains how to secure an Apache server with SSL/TLS hardening and best practices.