
How to Start Contributing to Metasploit: Field Notes from 68 Modules
68 modules in 2.5 years. Here's what the official docs don't tell you about writing Metasploit modules - from finding targets to surviving code review.
Your .swp Files Are Telling on You: A Git Forensics Guide
Swap files from Vim and nano can leak usernames, hostnames, and sensitive data in git repos. Even after deletion, the blob stays in git history forever. Here's how to find them and how to actually clean them.
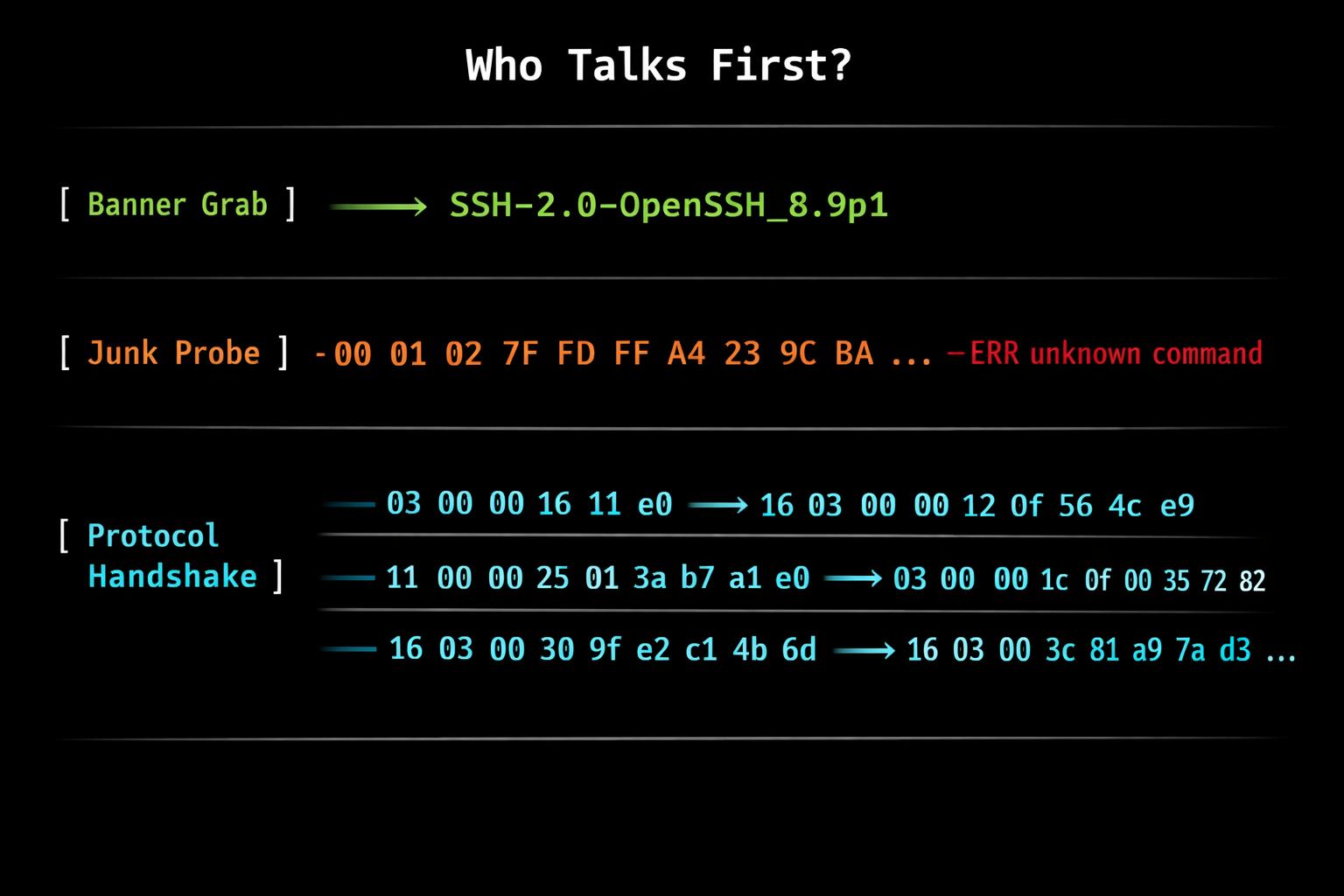
How Internet Scanners Actually Work: The 'Passive' Scanning Myth
A deep dive into how internet-wide scanners like Shodan, Censys, and nmap actually identify services. Spoiler: there's nothing passive about it.
Setting Up Giscus: An Ad-Free Alternative to Disqus for Blog Comments
How I set up Giscus for ad-free blog comments using GitHub Discussions, avoiding Disqus due to ads and other concerns.
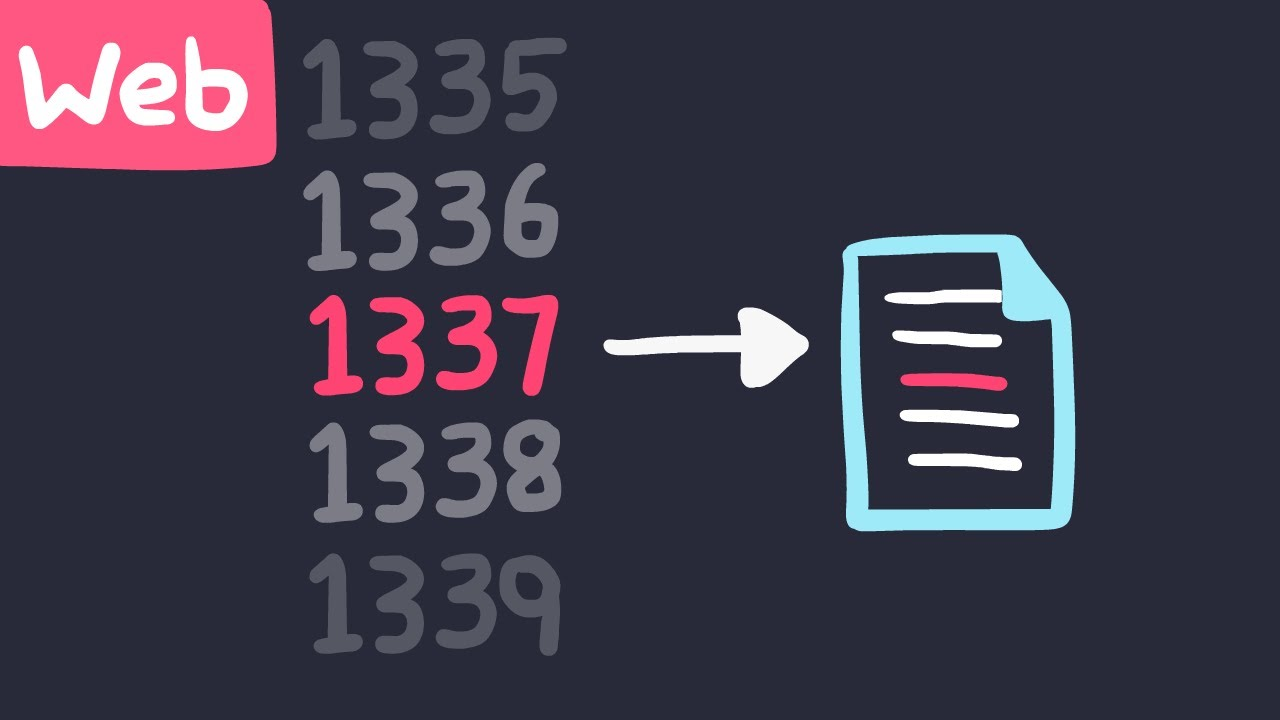
IDOR Vulnerability: Explanation, Exploitation, and Prevention
In this article, we will explore the Insecure Direct Object Reference (IDOR) vulnerability, a common security vulnerability in web applications that can have significant impacts on data confidentiality, integrity, and availability.
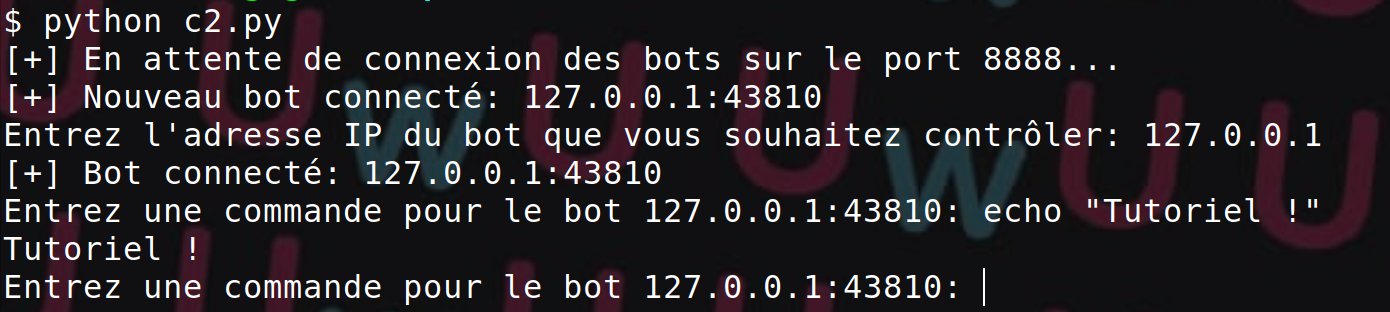
Using Python Sockets for Offensive Security
In this article, we will explore how to use Python sockets in the context of offensive security
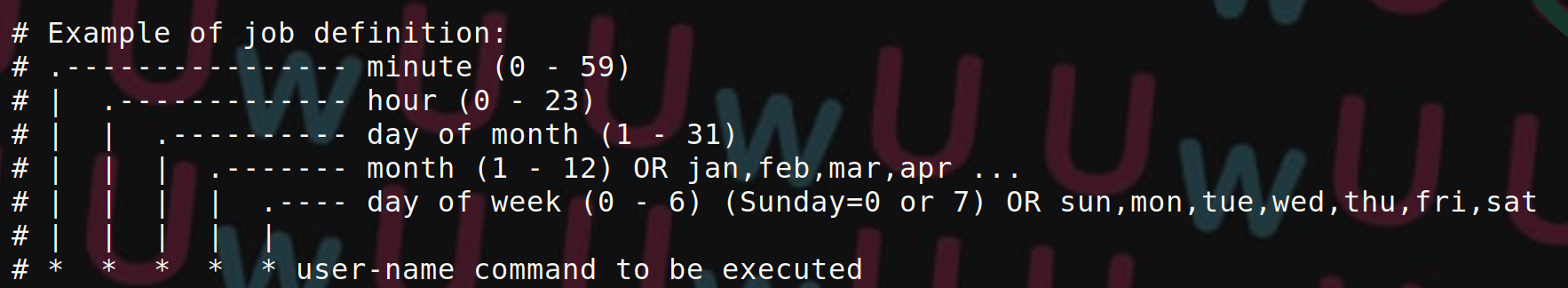
Privilege Escalation on Unix Systems via Crontab
This article demonstrates how to exploit privilege escalation from insecure scheduled tasks.

What is a Command Injection?
This article explains what command injection is, how to exploit it, and how to reduce the risks of this attack.

Configuring an Apache Server with SSL/TLS Hardening
This post explains how to secure an Apache server with SSL/TLS hardening and best practices.